OphionLocker Uses Next-Gen Encryption to Ransom Your Files
Posted by MOAAZ BUKHARI
“Ransomware is now one of the fastest growing classes of malicious software,” according to Kaspersky Lab’s Fedor Sinitsyn. “In the last few years it has evolved from simple screen blockers demanding payments to something far more dangerous.”
The latest type of ransomware uses almost unbreakable next generation encryption software, called elliptic curve cryptography, to encrypt all data on your computer – photos, videos, documents, illustrations, databases, everything. You receive a message saying that if you want your files decrypted, you have to pay the hackers, usually in bitcoin, by a certain deadline. CryptoDefence, CryptoWall, CryptoLocker and GpCode are some examples.
OphionLocker: A Highly Complex Threat
A new family of even deadlier encryptors was discovered by Kaspersky Lab at the end of June. What sets them apart is that the cybercriminals use the TOR anonymity network to cloak their command and control servers, and use a highly complex and unorthodox cryptographic algorithm to ensnare their prey. Critroni was the first one, but Trojan7Malware discovered another last week, dubbed OphionLocker.
How It Works
Hackers launch a malvertising campaign – dropping infected ads in regular ad networks. When you click an infected ad, or let it load in your browser, OphionLocker is activated. It contains an RIG exploit kit malware preloaded with exploits for different web browsers and plugins. The kit cycles through the exploits until one works, poisoning your computer. According to F-Secure, you get a message like this:
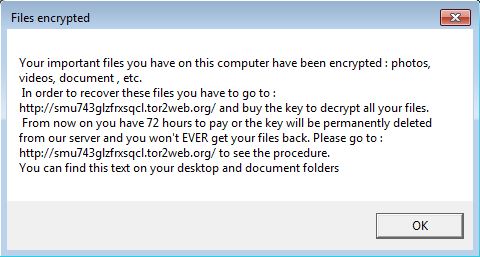
Many text files also pop up demanding the ransom. If you want your files back, you have to pay the hackers one bitcoin (about $350) within three days. To do so, you have to visit the mentioned URL hosted on the TOR network:
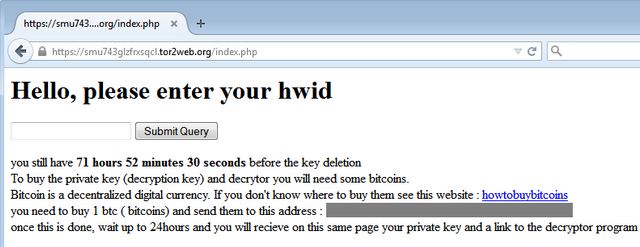
‘HWID’ stands for hardware identification, a unique number OphionLocker generates per infected computer. Victims pay for the decryption keys. Once you make the purchase and enter the keys, your files are restored.
Protecting Yourself:
Preventing OphionLocker is easier when you have a capable antivirus, like Kaspersky’s CryptoMalware Countermeasures. Also, remember to update your browser with the latest security patches to reduce the chances that the RIG exploit kit will deploy. Defeating OphionLocker, however, is difficult since it comes with a preloaded public key, allowing file encryption to even if there’s no internet connection. Once you make the payment, OphionLocker generates the corresponding private decryption keys (server side) and sends them to you.
The post OphionLocker Uses Next-Gen Encryption to Ransom Your Files appeared first on .



